From Awareness to Action: How Better Reporting Can Strengthen Cybersecurity
With schools across the nation experiencing a dramatic surge in ransomware attacks, data breaches, and operational disruptions, the education sector has become a prime target for cybercriminals. This growing issue not only affects IT, but also threatens student safety, instructional continuity, and financial stability. Schools and universities are widely viewed as soft targets, where chronic funding gaps leave critical vulnerabilities unaddressed and a culture of open information sharing can conflict with necessary security controls.
The data these institutions hold makes them especially valuable. Student records, health information, financial data, and IEPs, which are protected under state and federal privacy laws, represent high-value assets commonly targeted for exploitation. In higher education, government-funded research adds another layer of exposure, making institutions a target not just for one-time attacks, but for sophisticated intrusions that can go undetected for months. Effective cybersecurity reporting is the foundation of informed decision-making, institutional accountability, and the trust that students, families, and research partners place in schools every day.
Bridging the Language Gap
Many cybersecurity reports contain the right data, but deliver the information in the wrong language, and when reports fail to connect with leadership, even critical information can go unaddressed. The disconnect often comes down to translation. Technical teams typically communicate in the language they know, like severity scores, Common Vulnerabilities and Exposures (CVE) classifications, and patch windows, but not everyone in the room speaks that language. "The information within these reports is absolutely critical,” says Dr. Dawn Dunkerley, Principal vCISO, Edge. “But we're communicating it in a way that's difficult for non-technical leaders to absorb. Terms like ‘red team,’ ‘blue team,’ ‘penetration testing,’ and ‘vulnerability assessment’ may be precise within IT circles, but they don’t communicate value or urgency to presidents, superintendents, and boards. When leaders hear unfamiliar jargon, they often disengage because they can’t connect the terminology to their responsibilities.”
“Building a roadmap starts with understanding where quick wins are possible. Security awareness training, phishing simulations, asset inventory, incident response planning are all things that can be put on a roadmap and accomplished fairly quickly with leadership support. From there, you build toward more strategic initiatives, like security information and event management (SIEM) implementation, vendor risk assessments, and staffing decisions. In many cases, the longest pull is getting leadership to help enact the policies that allow you to do the work that needs to be done.”
– Dr. Dawn Dunkerley
Principal vCISO
Edge

 The goal isn’t to eliminate technical accuracy, but to provide context that makes technical findings actionable. That means connecting terminology to operational impact, financial exposure, and regulatory consequences. “If you're seeking funding for penetration testing, follow that up with a plain-language explanation: 'We are hiring experts to attempt to breach our systems,” explains Dunkerley. “If we fail to connect why leadership should care about what we need them to do, we risk losing their attention entirely, and with it, the resources and support needed to act. The goal is not to sacrifice technical precision, but to communicate that information verbally and visually in a way that provides the context necessary to drive informed decision-making."
The goal isn’t to eliminate technical accuracy, but to provide context that makes technical findings actionable. That means connecting terminology to operational impact, financial exposure, and regulatory consequences. “If you're seeking funding for penetration testing, follow that up with a plain-language explanation: 'We are hiring experts to attempt to breach our systems,” explains Dunkerley. “If we fail to connect why leadership should care about what we need them to do, we risk losing their attention entirely, and with it, the resources and support needed to act. The goal is not to sacrifice technical precision, but to communicate that information verbally and visually in a way that provides the context necessary to drive informed decision-making."
Quantifying Risk to Drive Action
Leadership needs cybersecurity reporting that answers their core questions and aligns with their responsibilities of student safety, operational continuity, fiscal stewardship, and regulatory compliance. “IT and cyber risk is not just an IT problem, but an operational risk,” says Dunkerley. “Painting a full picture starts with quantifying what a breach actually costs. Beyond the direct costs of rebuilding or purchasing new systems, overtime expenses, breach notification, legal fees, insurance involvement, and any associated fines, we are also seeing situations where institutions are not only losing grant funding, but are required to repay the federal government as well. There are also the indirect costs like insurance premiums increasing or losing coverage altogether. How do you put a number on reputational damage? But it absolutely carries a potential cost, especially in a resource-strained environment where a prospective student's family sees that a school just experienced a major breach. That may very well weigh on their decision."
Beyond risk quantification, leadership needs to understand the regulatory stakes. In higher education, Gramm-Leach-Bliley Act (GLBA) compliance is not optional, and the consequences of falling short are significant. "If you don't meet GLBA requirements, they have the right to remove your ability to process financial aid,” says Dunkerley. “These are the stakes we need to communicate. Are we briefing leadership on where we're improving? Where we're falling short, and why; whether that's a budget constraint or a staffing gap. We have to be able to convey why certain changes matter and why we need their support. Sometimes it's simply a matter of getting that support in place."
“IT and cyber risk is not just an IT problem, but an operational risk. Painting a full picture starts with quantifying what a breach actually costs. Beyond the direct costs of rebuilding or purchasing new systems, overtime expenses, breach notification, legal fees, insurance involvement, and any associated fines, we are also seeing situations where institutions are not only losing grant funding, but are required to repay the federal government as well. There are also the indirect costs like insurance premiums increasing or losing coverage altogether. How do you put a number on reputational damage? But it absolutely carries a potential cost, especially in a resource-strained environment where a prospective student's family sees that a school just experienced a major breach. That may very well weigh on their decision."
– Dr. Dawn Dunkerley
Principal vCISO
Edge

Creating a Reporting Framework
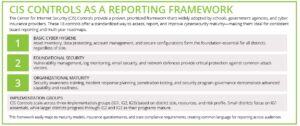
Effective cybersecurity reporting requires a common framework that leadership, insurers, and regulators can all reference. The Center for Internet Security (CIS) Controls provides a prioritized, widely adopted structure that enables institutions to assess their security posture, track progress over time, and communicate maturity in a consistent, credible way. “This framework is a great place to start, especially if you are running a less mature program, because it has the concept of implementation groups,” says Dunkerley. “Your first group covers the basics. Do you know what hardware and software you have on your network? Do you have access controls and secure configurations in place? From there, you build on that maturity level. Group two adds vulnerability management, logging, and monitoring. Group three gets into organizational maturity, like incident response planning, penetration testing, security awareness training, and program governance, which includes reporting to your board.”
“What makes this framework particularly useful for leadership reporting is its ability to show measurable progress over time,” continues Dunkerley. "You can show steady progress that the money being spent on people, processes, procedures, and tools is improving the organization. As a vCISO, I like to develop a work plan based on an initial assessment. We build a roadmap for the year, and by the end of it you can say here is everything we accomplished, and here is what we are focusing on next. That steady trajectory is something leadership can see, understand, and support."
To communicate complex security postures at a glance, cybersecurity dashboards offer a visual overview that is easy to understand. A well-designed dashboard highlights status, trends, and priority actions, where each control or risk domain receives a color-coded rating. “Dashboard reporting transforms raw security data into a clear, leadership-ready narrative that shows where progress has been made, where risks and gaps remain, and what concrete steps are needed to move forward,” explains Dunkerley. “Green means fully implemented and meeting security standards. Yellow is partially implemented with identified gaps requiring attention and red means critical gaps presenting immediate risk to operations or compliance. Among dashboard best practices include a ‘Last 90 Days’ trend indicator for each control area to show whether the district is improving, maintaining, or regressing. This view helps leadership understand momentum and program effectiveness.”
Moving from Snapshot to Roadmap
Effective cybersecurity reporting does more than document where an institution stands today. A maturity roadmap gives leadership a forward-looking view of where the program is headed, what resources are needed to get there, and how progress will be measured along the way; making it an essential tool for budget planning, grant applications, and board accountability. “Building a roadmap starts with understanding where quick wins are possible,” explains Dunkerley. "Security awareness training, phishing simulations, asset inventory, incident response planning are all things that can be put on a roadmap and accomplished fairly quickly with leadership support. From there, you build toward more strategic initiatives, like security information and event management (SIEM) implementation, vendor risk assessments, and staffing decisions. In many cases, the longest pull is getting leadership to help enact the policies that allow you to do the work that needs to be done.”
“What makes this framework particularly useful for leadership reporting is its ability to show measurable progress over time. You can show steady progress that the money being spent on people, processes, procedures, and tools is improving the organization. As a vCISO, I like to develop a work plan based on an initial assessment. We build a roadmap for the year, and by the end of it you can say here is everything we accomplished, and here is what we are focusing on next. That steady trajectory is something leadership can see, understand, and support."
– Dr. Dawn Dunkerley
Principal vCISO
Edge


That roadmap also makes the financial case for cybersecurity investment. Tools like the FAIR model and IBM's annual Data Breach Report can help quantify risk in terms leadership understands. "If you can show the average cost of a breach against the cost of a specific investment like multifactor authentication, you are making a financial case,” says Dunkerley. “We are actually seeing schools that have been working through their frameworks have their insurance premiums go down. Where others are seeing premiums rise because insurers view them as a risk. These schools can show their framework, demonstrate their progress, and explain the numbers. That is a direct, measurable return on investment.
Ultimately, the goal of every report, every dashboard, and every board briefing comes back to one thing. Cybersecurity is not about perfect technology, it is about reducing risk — never to zero, but reducing exposure — and helping everyone understand what is at stake. The institutions that get this right are not the ones with the biggest budgets. They are the ones where leadership and technology teams speak the same language and work together to move in the same direction."
At Edge, we believe cybersecurity can be both effective and affordable. Through our procurement platform, we offer a full suite of enterprise security services designed with colleges and universities, public school districts, and government entities in mind.
Ready to protect what matters most? Explore our tailored cybersecurity solutions at njedge.net/solutions/cybersecurity.
